Challenge: Eliminating dangling DNS records from a large public DNS presence
A U.S. healthcare company recently became aware that they were vulnerable to attack due to dangling DNS records that were active across their public DNS presence.
Dangling DNS records are obsolete or misconfigured entries in a DNS control panel that point to a domain or resource (such as an IP address, server, or cloud service) that either no longer exist or are no longer associated with the domain in question, such as a CNAME record pointing to a non-existent AWS resource.
Threat actors exploit dangling DNS records in several ways, including subdomain takeovers, traffic redirection, and cookie exploits that lead to adversaries authenticating themselves on corporate networks.
Our customer needed a fast and accurate appraisal of how exposed they were to these kinds of attacks, and immediately actionable intelligence on what records were dangling, so that their infrastructure team could resolve the problem before the organization suffered an attack.
Solution: Locating and removing 2,000+ dangling DNS records
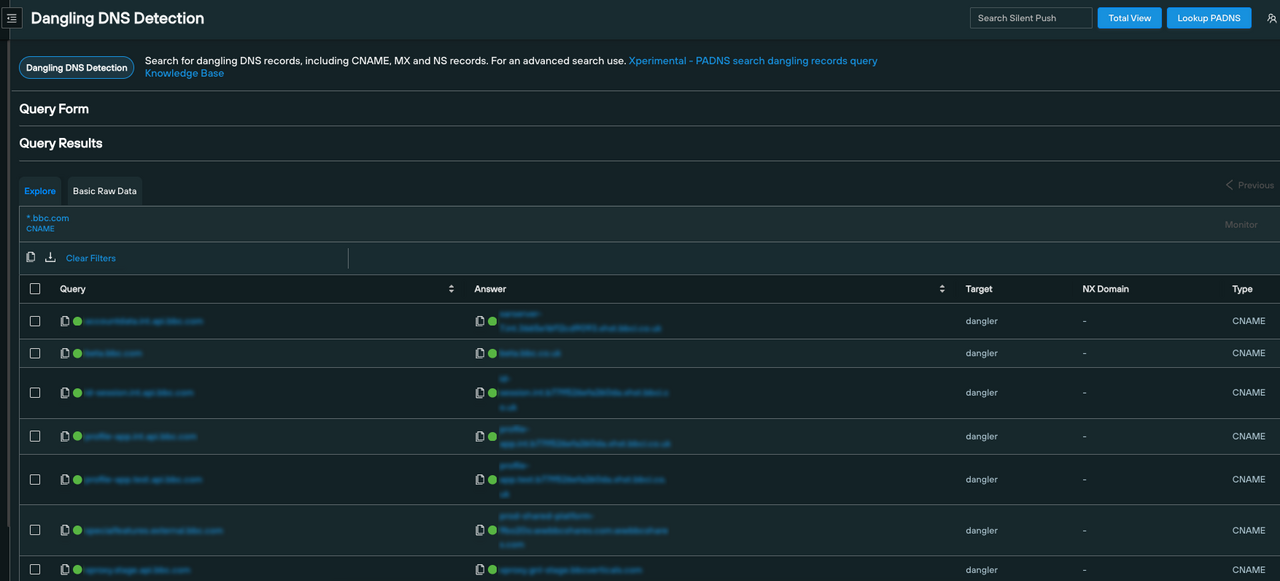
Silent Push Enterprise edition features a dedicated query that scans an apex domain, and outputs a list of all associated dangling DNS records, including the record itself and the associated subdomain.
Once a dangling record has been located, security teams are able to log into their organization’s DNS control panel and resolve the problem by removing or amending the record in question.
Immediately after completing onboarding, our customer ran a dangling DNS query and discovered 2,000+ exploitable DNS records that required immediate resolution before the company was targeted in a subdomain takeover.
Our customer used the data export feature to obtain the raw data on every exploitable record, before logging into their DNS control panel and remediating the problem by deprovisioning the required records and securing their attack surface from exploits.
The Silent Push Difference: Ready-made SOC and IR intelligence
Silent Push Enterprise and Community editions feature a bank of Attack Surface Mapping queries that are designed to provide SOC, IR and Infrastructure teams with immediately actionable intelligence and insights on potential vulnerabilities.
Silent Push Enterprise customers have access to dedicated dangling DNS records, and scans that reveal 3rd party services linked to a network.
Our customer was unaware of how exposed they were before they came onboard with Silent Push, and were able to not only remediate an urgent dangling DNS issue, but automate the query to run every 24 hours so that the team are kept constantly in the loop about any exploitable records that may appear in the future.
Silent Push knows more about global Internet-facing DNS infrastructure than any other provider, which gives our customers the ability to fully enumerate any given attack surface or threat landscape and preemptively resolve exploitable DNS records before they appear on a threat actor’s radar.
Learn More About Our Unique Approach to Preemptive Threat Intelligence
Find out how Silent Push helps you to locate hidden and known threat infrastructure, and stop digital assaults at the source before they occur using Indicators Of Future Attack (IOFA)™
IOFA™ are domain and IP datapoints that preemptively pinpoint adversary intent BEFORE an attack is launched, and reveal searchable digital fingerprints of attacker activity.
Contact us here for more information, or to discuss how we can help you expose dangling DNS records.
Further Resources
Our CTO, John Jensen, provided extensive analysis of dangling records and subdomain takeovers in his talk at the VirusBulletin conference 2023. Click here to view the presentation and download the research paper.
We’ve also blogged about the persistent problem of subdomain takeovers, and how dangling DNS records are a backdoor onto corporate networks. Click here to read our research.



